The Restrict Access to IP Address Range assertion restricts or allows service access based on the IP address of the application requestor.
The IP address of the requestor considered when this assertion is run can either be the actual remote IP address available at the TCP level or a string extracted from the message. The latter case can be used, for example, when requests are first forwarded through multiple network components before arriving at the Gateway. If such network components are configured to pass down the original IP address through an HTTP or SOAP header, that information source can then be configured in the Restrict Access to IP Address Range assertion using context variables.
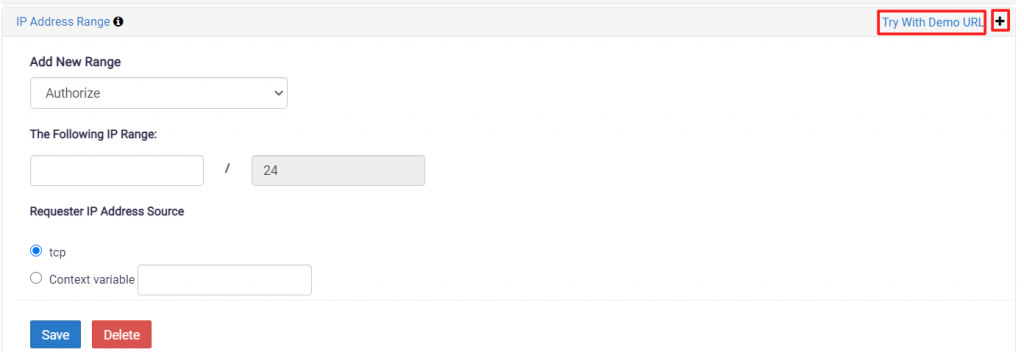
Configure the assertion as below:
- Authorize/Forbid
From the drop-down list, select Authorize if you are permitting access to the IP range listed. Select Forbid if you are restricting access to the IP range listed. - IP range
Enter the allowable or forbidden IP address. Both IPv4 and IPv6 addresses are supported. - Requestor IP address source
Specify how the Gateway should determine the source IP address:- Select TCP to use the IP address associated with the TCP request.
- Select the Context variable and then enter any context variable that resolves to a valid IP address. The default is request.tcp.remoteAddress, which will return the remote address of the TCP connection through which the message arrived.
Click on Save to complete the configuration. To restrict multiple IP ranges, click on the “+” button. A new section will appear to add IP range. Hit Try with Demo URL to check how assertion work.
